Kraken Phishing Analysis - Search Adverts and Non-validated URL Redirect Exploits
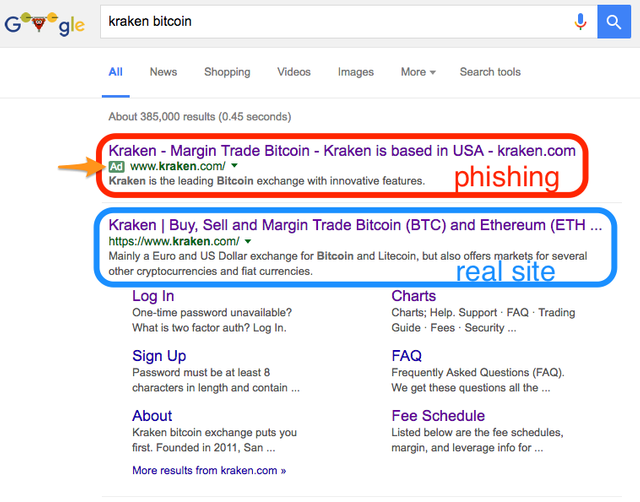
Recently Kraken issued a warning on it's blog[1] regarding various phishing attacks that has caused some accounts to lose their Bitcoin.
I decided to do some research in to how this could have happened as my previous knowledge of advert networks say that this isn't possible otherwise it would be much more commonplace.
The advert display networks allow you to customize[2] the 'Display URL' vs the 'Destination URL'. The Display URL is what the user will see and the Destination URL is where the advert will take the user when clicked. This is allowed because some websites have user unfriendly URL's. There are limitations on this and that is the Display URL root domain must match the Destination URL root domain. For example:
Approved URL customizations
| Display URL | Destination URL |
|---|---|
| Steemit.com | https://www.steemit.com/signup?adref=gadws_campaign1 |
| SignUp.Steemit.com | https://www.steemit.com/signup?adref=gadws_campaign2 |
| Steemit.com/Signup | https://signup.steemit.com |
Unapproved URL customizations
| Display URL | Destination URL |
|---|---|
| Steemit.com | https://steem.io/join |
| SignUp.Steemit.com | https://steemd.com/signup/ |
| Steemit.com/Signup | https://steemit.steem.io |
This is a very interesting and more sophisticated phishing attack in that the attackers seem to have utilized a possible open redirect flaw[3] in the Kraken website to bypass anti-phishing mechanisms on the Google, Bing and Yahoo advert display network.
Kraken have yet to confirm whether this is the case or how it happened but testing the redirect feature (https://www.kraken.com/redirect?url=INSERT_URL_HERE) after the event seems to throw a few errors ranging from generic 403 Forbidden messages to generic CloudFlare 'You have been blocked' messages. This leads me to believe this is a temporary "duck-tape" solution to mitigate the issue.
Why do I believe it is a temporary "duck-tape" solution? Because of the generic standard errors that it produces. If the attack vector was considered at the beginning then usually a more user-friendly approach is taken; such as a custom error message with company branding. This is only an assumption on my part.
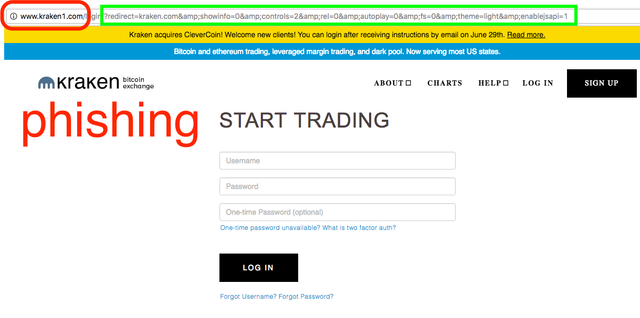
However the phishing site has an interesting string in the URL (highlighted in green by me). This correlates somewhat to the same redirect feature on the official website and knowledge of other websites that have these vulnerabilities has shown me that the query string or other data from the original function tend to be passed to the destination, such as source along with other neccessary parameters.
No evidence of Kraken itself being hacked
- Kraken
Unless the attacker found a flaw in Google, Yahoo and Bing then the only thing that would allow Display URL's with the Kraken domain would be a redirect exploit on one of the kraken.com domain names.
One thing to be aware now is to skip the adverts in search engines and only use known links to websites.
Thoughts?
Footnotes
1: http://blog.kraken.com/post/148976188862/kraken-phishing-warning
2: https://adwords.googleblog.com/2006/05/display-vs-destination-urls.html
3: https://www.owasp.org/index.php/Testing_for_Client_Side_URL_Redirect_(OTG-CLIENT-004)
Checksum: d04d058e57ce92bf697f7c233a8061bce1210a4b